Mythos Changes the Threat Model
Anthropic’s Mythos has sharpened a hard truth: cyber capability is becoming easier to concentrate and operationalise. For SMEs, that means ambiguity is getting more expensive.

Expert analysis, security guides, and company news to help you stay ahead of the curve.
Anthropic’s Mythos has sharpened a hard truth: cyber capability is becoming easier to concentrate and operationalise. For SMEs, that means ambiguity is getting more expensive.


£20 a month. A team who answered at midnight. And the end of staring at the ceiling wondering if today was the day it all fell apart.

I used to think being small made us vulnerable. It does. But it also makes us fast, adaptable, and capable of change the big players can only dream of.

Four years. One password. Zero excuses. Here's how we went from security disaster to actually knowing what we were doing.

Honest time expectations
I've sat where you're sitting.

The impossible middle ground we all live in

I knew we had a problem when I found Kev's password written on a Post-it note stuck to his monitor.

Working with informal support

The hidden tech requirements that nearly cost us everything - and how to spot them before it's too late.

The real cost of Cyber Essentials certification - beyond the website price. What nobody tells you about the time, the stress, and the emergency biscuit runs.

Supply chain security questions used to terrify me. Now I help businesses answer them. Here's what the big firms actually want to hear - and how to say it with confidence.

I used to be a security disaster. Then I met TransCrypt. This is what three years of change looks like - and the one habit I still can't quite break.

You've got Cyber Essentials. Your accountant's still using 'Password1'. Here's how to have the conversation without losing the relationship.

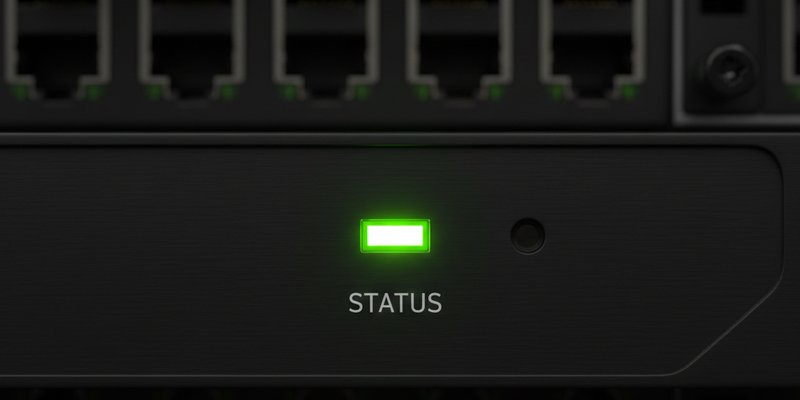
One protects you from attacks. One helps you recover when protection isn't enough. Here's why you need both - and which one to get first.

You don't need an IT department to get Cyber Essentials certified. You need a starting point and the willingness to learn. Here's proof.

Your staff aren't your security weakness. Your training gap is. Here's how to turn your team from liability into your strongest defence.

Starting point for every confused business owner

Positive outcomes and motivation
A forensic critique of "Security Theatre" and the failure of the "Paper Shield" audit model. We define the shift toward Deterministic Compliance—moving the burden of proof from subjective human testimony to real-time mathematical verification.

Firewalls, secure configuration, access control, malware protection, patch management. Sounds complicated. It isn't. Here's what they actually mean and why they matter.

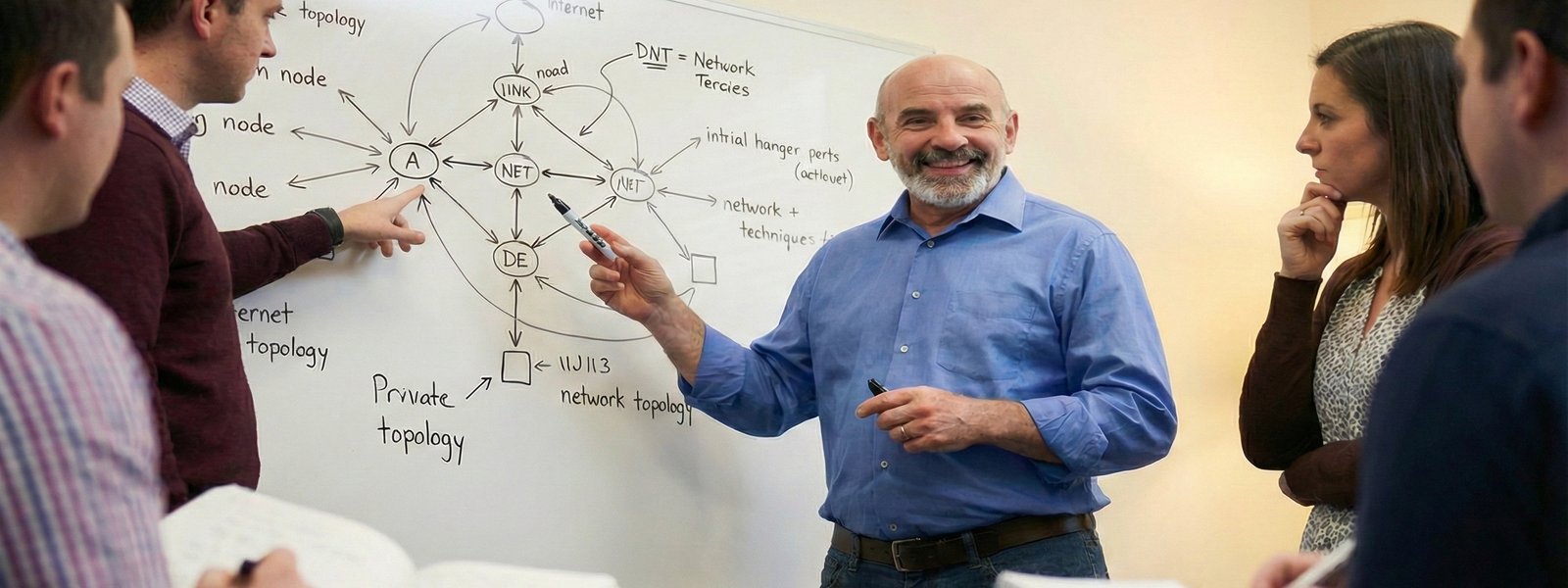
TransCrypt's platform combines AI reasoning with deterministic logic. Translation: it's smart enough to guide you and reliable enough to trust. Here's how it actually works.

Your clients all need Cyber Essentials. You can't clone yourself. Here's how MSPs are scaling compliance without burning out.

You've got Cyber Essentials. Now everyone's asking about Plus. Here's what's different, what's involved, and how to know if you actually need it.

Government contracts changed our business. They're not just for the big players - but you need to know the rules. Here's everything we learned the hard way.