Mythos Changes the Threat Model
Anthropic’s Mythos has sharpened a hard truth: cyber capability is becoming easier to concentrate and operationalise. For SMEs, that means ambiguity is getting more expensive.

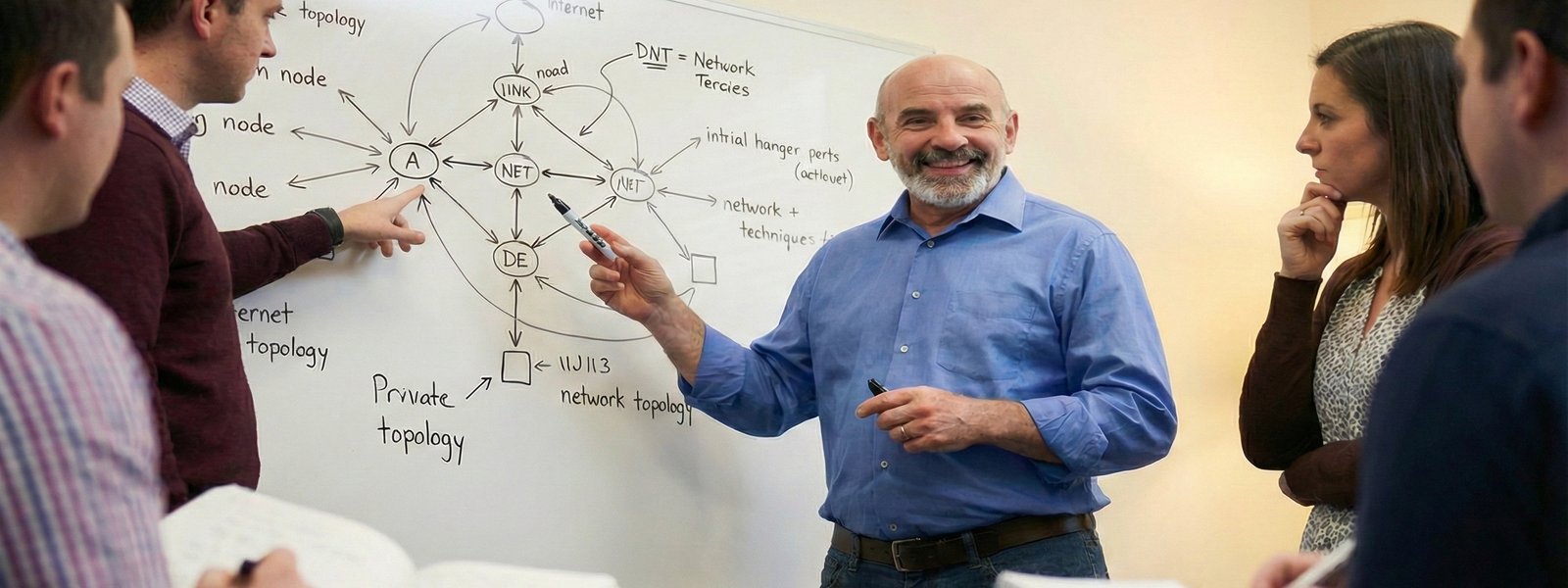
Robust security operations for growing teams and rapid expansion.
Anthropic’s Mythos has sharpened a hard truth: cyber capability is becoming easier to concentrate and operationalise. For SMEs, that means ambiguity is getting more expensive.


Anthropic’s Mythos has sharpened a hard truth: cyber capability is becoming easier to concentrate and operationalise. For SMEs, that means ambiguity is getting more expensive.

Four years. One password. Zero excuses. Here's how we went from security disaster to actually knowing what we were doing.

Your clients all need Cyber Essentials. You can't clone yourself. Here's how MSPs are scaling compliance without burning out.

Supply chain security questions used to terrify me. Now I help businesses answer them. Here's what the big firms actually want to hear - and how to say it with confidence.

One protects you from attacks. One helps you recover when protection isn't enough. Here's why you need both - and which one to get first.
A forensic critique of "Security Theatre" and the failure of the "Paper Shield" audit model. We define the shift toward Deterministic Compliance—moving the burden of proof from subjective human testimony to real-time mathematical verification.