What actually happens, what they actually ask, and why you're going to be fine
Your First Audit: A Survival Guide
I need to tell you about Kev and the tie.
The day before our first technical audit, Kev came up to me looking genuinely worried. This is a man who's been in the lubricants business for thirty years. Seen everything. Unflappable.
"Danny," he said. "Should I wear a tie tomorrow?"
That's what audits do to people. They make sensible adults completely lose perspective. Suddenly everyone's panicking about dress codes and whether the office is tidy enough and if the auditor is going to find that one folder from 2019 that nobody's opened since.
I've been through a fair few audits now. First one was terrifying. Second one was nerve-wracking. By the third, I was actually looking forward to it.
Here's everything I've learned. The stuff I wish someone had told me before that first one.
What an Audit Actually Is
Let's start with the basics, because I think people have the wrong mental image.
A technical audit isn't an interrogation. Nobody's trying to catch you out. There's no "gotcha" moment where they dramatically reveal your failures and everyone gasps.
It's a verification exercise. You've said you do certain things - have firewalls, manage access, update software. The auditor is checking that you actually do those things. That's it.
Think of it like a driving test, but you've already been driving for months and the examiner just wants to confirm you know what you're doing. They're not hoping you fail. They want you to pass. Their job is to verify, not to destroy.
What They're Looking For
For a Cyber Essentials Plus audit - which is what most small businesses will face - they're checking the five controls:
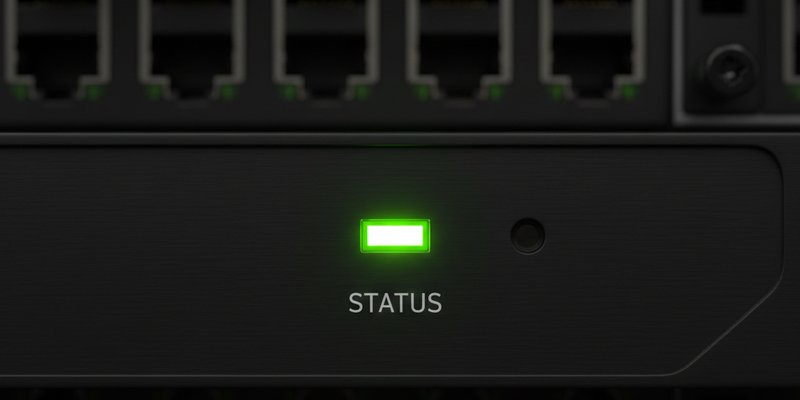
Firewalls: Is there one? Is it configured properly? Can they see evidence it's doing its job?
Secure Configuration: Are your devices set up securely? Default passwords changed? Unnecessary stuff removed?
Access Control: Do people have their own accounts? Are admin rights restricted? Is there a process for leavers?
Malware Protection: Is anti-virus installed and running? Is it up to date? Is it set to scan automatically?
Patch Management: Are your systems updated? Within the required timeframes? Can you show evidence?
That's what they care about. Not whether your desk is tidy. Not whether Kev's wearing a tie. Just: do you actually do the things you said you do?
Before the Audit
Right, practical stuff. Here's how to prepare without losing your mind.
Two weeks before:
Gather your documentation. Policies, procedures, the stuff you said you have. Make sure you can actually find it. Nothing worse than saying "yes, we have a password policy" and then spending twenty minutes trying to locate it.
Do a self-audit. Go through the five controls yourself. Check everything. Pretend you're the auditor. What would you ask? What evidence would you want to see?
Fix anything obvious. If you find a laptop that hasn't been updated, update it. If someone's still using a default password, change it. Don't leave easy points on the table.
One week before:
Brief your team. Not a big scary meeting - just let them know an auditor's coming, what they might be asked, and that it's fine to say "I don't know, let me check" rather than guessing.
Test your evidence. Can you actually demonstrate your controls? If you say you do weekly backups, can you show the backup logs? If you say software updates happen within 14 days, can you prove it?
Prepare a quiet space. The auditor will need somewhere to work, possibly to do some technical testing. A meeting room, a spare desk, somewhere without constant interruptions.
The day before:
Get some sleep. Seriously. You've done the preparation. Panicking now won't help.
Resist the urge to make last-minute changes. This is how mistakes happen. If your systems have been working fine, don't suddenly reconfigure everything the night before.
Tell Kev he doesn't need to wear a tie. Unless he wants to. It's a free country.
On the Day
When they arrive:
Be normal. Offer them a tea or coffee. Show them where the toilets are. They're a person doing a job, not an alien species.
Have someone available to answer questions - probably whoever knows the technical stuff best. At Simpson & Sons, that was me. Mr S was there for business context, but I handled the nitty-gritty.
During the audit:
They'll probably start with an interview. Questions about your processes, how you handle things, who's responsible for what. Answer honestly. If you don't know something, say so - "I'm not sure, let me check" is a completely valid answer.
Then there's usually technical verification. They might scan your systems, check configurations, look at actual evidence of your controls working. This is where your preparation pays off.
Don't hover nervously. Give them space to work. Be available for questions, but you don't need to watch every keystroke.
If they find something:
Stay calm. A finding isn't a failure. Most audits have findings - things that need minor attention or clarification.
Ask questions. What exactly is the issue? What would resolve it? Is it critical or minor?
Don't argue. If they've found a genuine gap, acknowledge it. The goal is to fix it, not to win a debate.
What They'll Probably Ask
Based on every audit I've been through, here are the questions that come up every time:
"Can you show me your password policy?"
Have it ready. Know where it is.
"How do you handle someone leaving the company?"
Be able to explain the process - removing access, changing shared passwords, etc.
"When was the last time you updated [specific software]?"
Be able to show evidence. Update logs, timestamps, something concrete.
"Who has admin access?"
Know the answer. Have a list.
"What happens if you detect a security incident?"
Have an incident response process - even a simple one - and be able to explain it.
"Can you show me your firewall configuration?"
Know how to access it. Know what the settings mean, broadly.
None of these are trick questions. They're checking that you actually do what you say you do.
Common Mistakes
I've seen businesses trip themselves up in completely avoidable ways:
Over-complicating answers. When they ask a simple question, give a simple answer. Don't ramble into every edge case and hypothetical. "Yes, we use Windows Defender, it updates automatically, here's where you can see it" is better than a fifteen-minute explanation of your entire security philosophy.
Pretending to know things you don't. If you don't know how the firewall is configured, say "I'm not sure, let me check" or "Danny handles that, let me get him." Guessing wrong is worse than admitting uncertainty.
Panicking over minor findings. If they find something small - a laptop that's a few days overdue on updates, a user account that should have been removed - it's not the end of the world. Note it, fix it, move on.
Being defensive. The auditor isn't your enemy. They want you to pass. Work with them, not against them.
After the Audit
If you pass:
Celebrate. You've earned it. Maybe some biscuits.
Keep doing what you're doing. Certification isn't a one-time thing - you need to maintain those standards.
Review any minor findings. Even if you passed, there might be recommendations. Take them seriously.
If you don't pass first time:
It happens. It's not the end of the world.
Understand exactly what the gaps are. What needs to change?
Fix the issues. Usually you'll have time to remediate and be re-assessed without starting from scratch.
Learn from it. What did you miss? How can you be better prepared next time?
The Kev Update
In case you're wondering: Kev did not wear a tie.
He wore his normal work shirt. The auditor didn't care. They asked him a few questions about how he handles suspicious emails (he's actually really good at this now), and that was it.
Afterwards, he said the whole thing was "a lot of fuss over nothing." Which, honestly, is the best possible outcome.
The Real Secret
Here's what I've learned after multiple audits:
If you've genuinely implemented the controls - not just on paper, but actually done them - the audit is just confirming what's already true.
The businesses that struggle are the ones who've ticked boxes without really doing the work. Who have policies they've never read. Who said they do things they don't actually do.
If you've done the work, the audit is a formality. A slightly nerve-wracking formality, but manageable.
Prepare properly. Be honest. Stay calm. You've got this.
And tell Kev he can leave the tie at home.
Danny Preece is Head of Technical Sales at Simpson & Sons and an SME Cyber Resilience Consultant with TransCrypt. He's been through seven audits now and only panics a little bit each time. Kev still asks about the tie thing as a running joke.
Ready to streamline your compliance?
Join hundreds of fast-growing fintechs building with Transcrypt today.
Join the WaitlistAbout the Author
"We are building the operating system for compliance. Transcrypt removes the ambiguity from regulatory frameworks, turning them into deterministic, executable code."