Moving from the subjective "theatre" of security consulting to the objective reality of binary logic schemas.
Content:
The industry has a secret: most compliance certifications are a performance. We call it The Drama. It is a seasonal ritual—an expensive, frantic exercise in manual evidence gathering, Slack-thread archaeology, and subjective interpretation. In this model, an audit is a snapshot in time, a narrative written to convince an assessor that your security posture matches your policy. It is a system built on "best efforts," and it is failing.
The Failure of Interpretation
Traditional audits rely on human judgement. When an auditor asks for proof of "secure configuration," they are often met with a curated screenshot or a signed PDF. This is not proof; it is testimony. The moment that screenshot is taken, the system state it represents begins to decay. By the time the certificate is issued, the underlying reality has shifted. This creates a "Paper Shield"—a certificate that satisfies a procurement department but provides zero technical assurance.
Determinism: Compliance as a Function
At Transcrypt, we treat compliance as a deterministic system. In computer science, a deterministic function is one where the same input always produces the same output. There is no randomness, no "spirit of the law," and no room for debate.
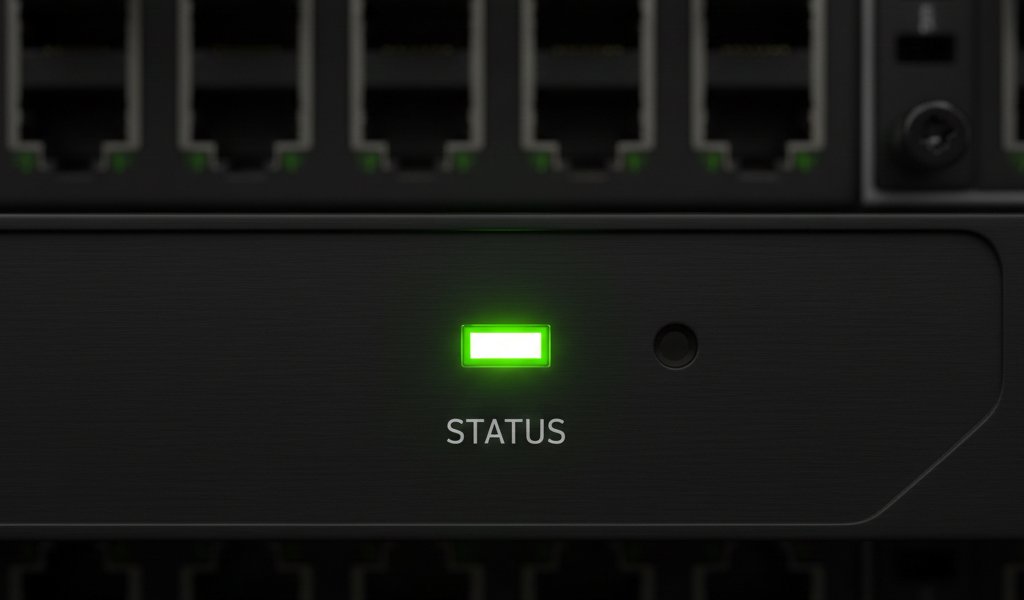
We replace the consultant’s interview with a Deterministic Rule Engine. When your system state is ingested via API—whether from AWS, Azure, Okta, or Jamf—it is not "reviewed." It is calculated. We map raw telemetry against rigid logic schemas.
- The Input: Cryptographically hashed system logs and configuration telemetry.
- The Logic: A binary schema defined by Cyber Essentials or ISO 27001 requirements.
- The Output: A pass or a fail.
The Mathematics of Truth
By moving the burden of proof from essays to maths, we establish a Verifiable Assurance Architecture. When compliance is a calculation, the "Panic of the Audit" disappears. You no longer "get ready" for an auditor because the maths is always running in the background.
If a security control fails at 03:00 on a Tuesday, the logic engine identifies the drift immediately. You do not wait six months for a sampling exercise to uncover the vulnerability. You catch it because the equation no longer balances.
Beyond the Snapshot
The "Missing Middle" isn't a better portal; it’s a better philosophy. We are moving away from the era of "trust me" and into the era of Provable Truth. By removing the drama of human interpretation and replacing it with the cold, reliable precision of a rule engine, we provide the only thing that actually matters in security: a matter of fact.
Ready to streamline your compliance?
Join hundreds of fast-growing fintechs building with Transcrypt today.
Join the WaitlistAbout the Author
"We are building the operating system for compliance. Transcrypt removes the ambiguity from regulatory frameworks, turning them into deterministic, executable code."